WANNACRYPT AND RANSOMWARE: HOW TO STAY SAFE
What is WannaCrypt/Wannna Cry?
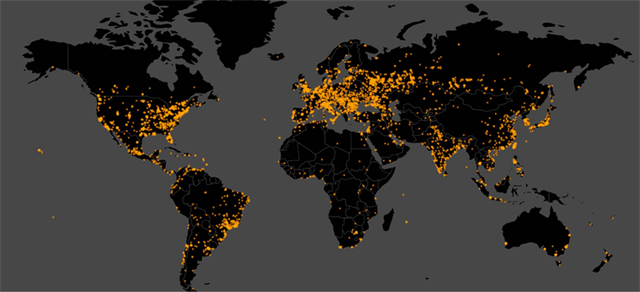
WannaCrypt is a piece of ransomware targeting computers operating systems. Beginning May 11, WannaCrypt was used in a major cyber-attack, impacting computers worldwide.
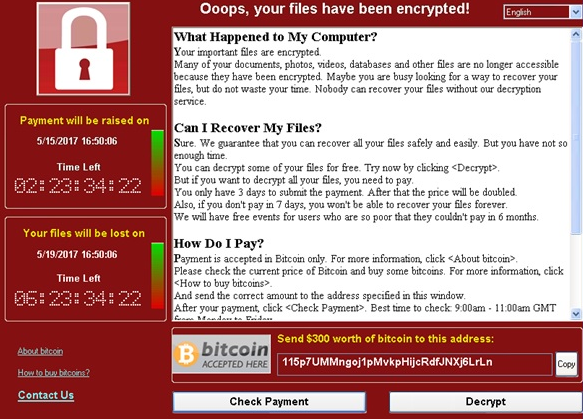
Once WannaCrypt infects a computer, it encrypts a user’s files so they cannot be accessed. WannaCrypt can infect a variety of file types, including .jpg, .doc, .txt, .csv, .png, .docx, .psd, .mp3, .pdf and more.
WannaCrypt hit many high profile organizations including the UK’s National Health Service (NHS), Vodafone, Telefonica, FedEx, and more. As a result of the attack, NHS doctors and nurses used pens and paper since they could not gain access to medical records and data. Although it is unclear why, Europe has been hit much harder than the U.S.
Users can regain access to their files by paying a ransom, usually around $300-$600. The ransom must be paid in Bitcoin.
How WannaCrypt Infects Computers
WannaCrypt initially spread via email attachment. Specifically, users open an email (often from a trusted source, like a co-worker, family member or friend) containing an attachment with the ransomware.
After opening the initial email, WannaCrypt spreads to machines with SMB exposed. It can also spread across internal networks once one machine is infected.
The ransomware uses a SMBv2 exploit originally discovered by the NSA (codenamed “ETERNALBLUE”). This exploit, along with several others, was patched by Microsoft on March 14 in the March Security Rollup. Because Microsoft quietly released the patch, the public didn’t learn about the issue until the website Shadow Brokers leaked the NSA’s code for this exploit in April.
Initially, Microsoft did not release patches for Windows XP, Windows 8, and Windows Server 2003, since they are out of support. However, in a highly unusual turn of events, the company released patches for those systems on May 12. (Windows 8.1 received the patch; Windows 8.0 did not.) The patches are available as a manual download.
How to Protect Yourself Against WannaCrypt (and Other Ransomware)
- Ensure your systems are up to date. Microsoft recommends upgrading to Windows 10, as it includes the latest safety features.
- Install security patches for WannaCrypt and other ransomware viruses.
- Be cautious! Even if you receive an email with an attachment from someone you know, don’t be afraid to verify the email was sent by the person you think it was. (Hackers are excellent at spoofing emails – making an email look like it’s coming from someone you know, when it’s really coming from someone else.)
- Back-up, back-up, back-up. Make sure you have a complete, updated backup of your files. (Your organization should also have an organization-wide policy in place, protecting user’s files. If you’re struggling to develop a comprehensive backup strategy, we can help.)
- Run regular ransomware/virus tools on your system to ensure you’re not missing something.
- Stay on top of updates and patches that are released for your system. WannaCrypt is (mostly) under control for now, but you can expect another ransomware attack to hit soon.
At SWICKtech, we have been working hard to ensure our clients are fully protected against WannaCrypt, and have been investigating the SMBv2 exploit since April. Because ransomware attacks will likely continue, our technical environment meets the highest standards. It includes multiple layers of security, patching and anti-virus protection, web filter and best practice firewall configuration. We also have robust, proactive maintenance procedures designed to protect clients from ransomware attacks while significantly reducing risk.
If your organization is struggling with WannaCrypt, or another ransomware, and needs assistance keeping your data safe, contact us to learn how we can help.