Microsoft warned its users last week about cloud application-based attacks that have grown in frequency since the global pandemic forced organizations to work remotely in March.
In a blog post, Microsoft Partner Group PM Manager Agnieszka Girling explains that in response to a demand for employee remote capabilities, cloud services and apps have been scaled up. “While application use has accelerated and enabled employees to be productive remotely, attackers are looking at leveraging application-based attacks to gain unwarranted access to valuable data in cloud services,” says Girling.
CONSENT PHISHING
You might be familiar with the more traditional Email Phishing Attacks where threat actors lure victims into giving up passwords and credentials. Consent Phishing Attacks, in contrast, trick victims into providing malicious Office 365 OAuth applications access to their Office 365 accounts and sensitive data or resources.
According to Microsoft, attackers are registering malicious apps that seem legitimate with an OAuth 2.0 provider like Azure Active Directory to make them seem trustworthy. The attacker gets a link to the malicious app in front of victims through traditional phishing techniques. The victims click, accept permissions and the attacker has access to their email, files, contacts, notes, and profile.
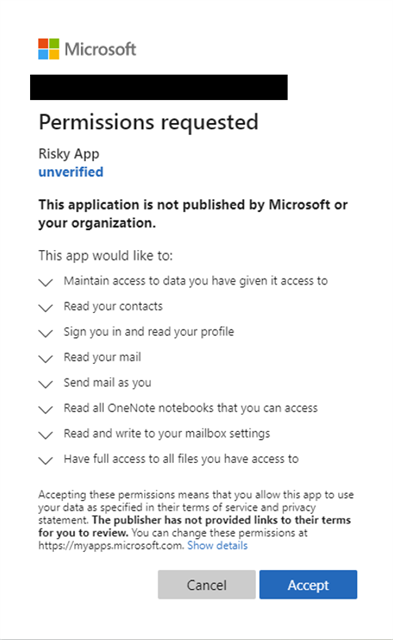
Example from Microsoft of permissions requests made during consent phishing attacks
MICROSOFT TO INVEST IN ADDITIONAL SECURITY
Girling says Microsoft is continuing to identify, disable and prevent use of malicious apps when it finds signs of them. “We’re also continuing to invest in ways to ensure our application ecosystem is secure by enabling customers to see policies on the types of apps users can consent to as well as highlighting apps that come from trusted publishers.”
THREE WAYS TO PREVENT CONSENT PHISHING ATTACKS
- Make sure you recognize the app name and domain URL before downloading
According to Microsoft, attackers use names that make the malicious apps appear to come from legitimate companies. Be sure to educate your staff on spotting phony URLs in emails. Also, keep an eye out for incorrect spelling and grammar.
- You are safe with Publisher Verified apps.
When an application is marked as Publisher Verified, it means their identity has completed a verification process in the Microsoft Partner Network and apps are safe to use. A blue badge will appear on the Azure AD consent prompt.
- Educate on and Audit Permissions and Consent
Microsoft says that organizations must understand the data and permissions an application is asking for and understand how permissions and consent work in Microsoft’s platform. Be sure your employee applications are accessing only the data needed and ensure administrators know how to manage and evaluate requests.
At SWICKtech we’re helping organizations put into place a multi-layered security approach that protects against and monitors for malicious activity across any business network. If you’re concerned about or want to learn more about protecting against consent phishing attacks, schedule a no-strings-attached consultation today.




